
PHP is often used in conjunction with HTML to produce dynamic results. One common use-case is registration forms. The registrant completes a form and submits it. Then, the PHP script will process the information and generate an output page, usually confirming the user's registration. Naturally, this is usually accompanied by saving the data to a backend application/database to track registrants, but we won't be doing that this time
One very important aspect to accepting data input 'from the wild' is security. It is critical that you anticipate user blunders and malicious attempts to break your application. We'll look at how to sanitize data before committing it to the application or database
Let's Go!
The scenario here is that the front-end team has handed off a registration page for your client's upcoming conference. Your job is to develop the backend processing page that will calculate registrants' fees and provide them a confirmation number
We've got several files and folders, here. But most of them are completed already. The one we'll be concerned with is the php/confirm.php page
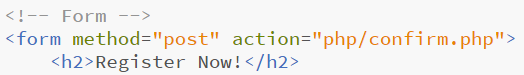
Notice here that we're using the POST method to submit the form
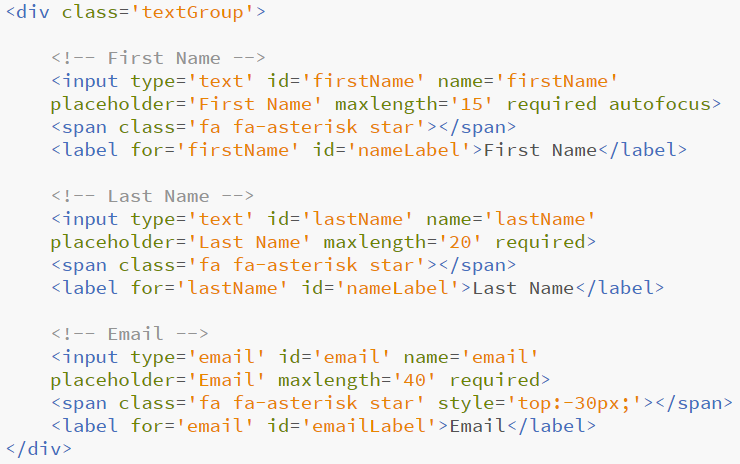
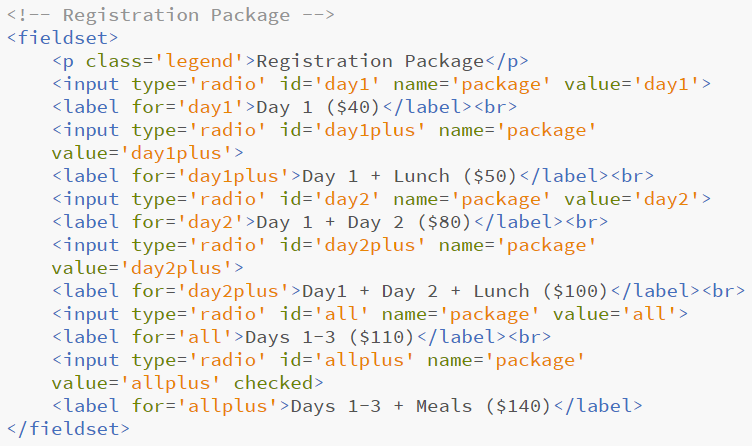
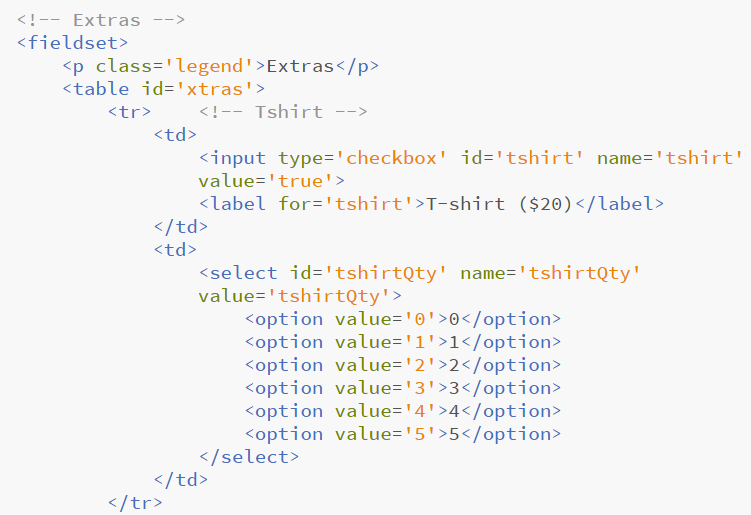
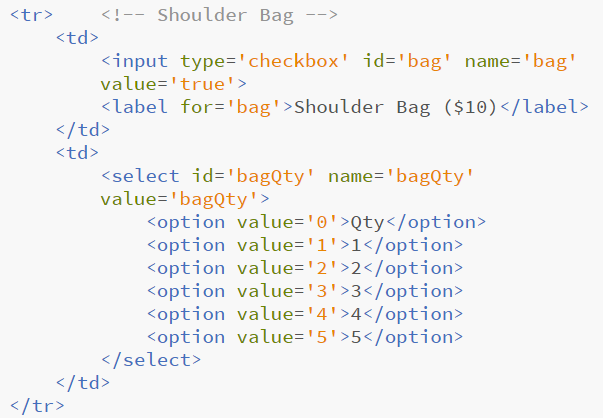
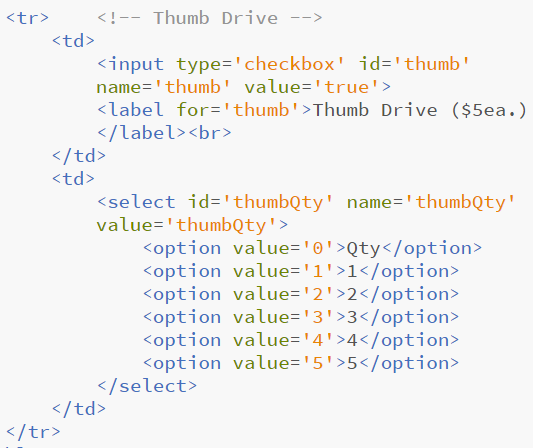
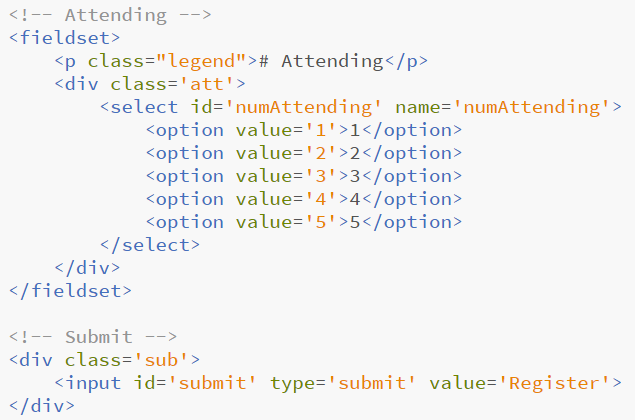
The important attributes/values for us with regard to the backend processing are name and, for the radio buttons/checkboxes/select lists, value. These are the key/value pairs that will be sent to the processing script when the form is submitted
I left the comments in to help guide us through the remainder of the lab
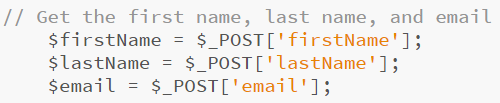
Remember, we're using the POST method, which sends the input data to the server in an associative array whose name is $_POST. So to pluck each value out, we call the appropriate key, which corresponds to the name attribute in the form
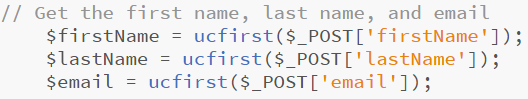
PHP has a built-in method called ucfirst(); which, oddly enough, will change the first letter of a string to uppercase
A critical security issue when you're handling user input is ensuring that the data is safe before it hits the server. PHP has built-in methods to help us with that, as well
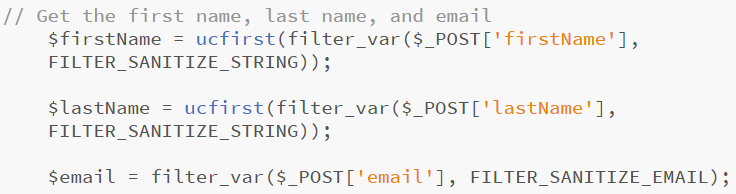
The filter_var method takes two paramaters (plus options, which we're not using here) - the input string (e.g., $_POST['firstName']) and the (globally defined) filter (e.g., FILTER_SANITIZE_STRING). It will return either a sanitized input or FALSE (if the filter fails). Notice that we used a different filter for the email input
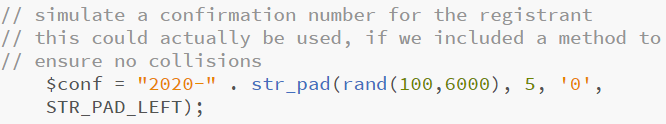
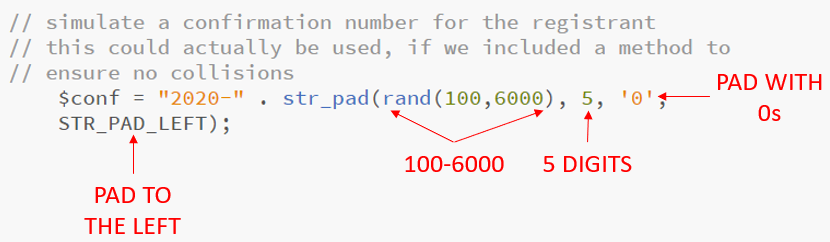
So, what's going on here?
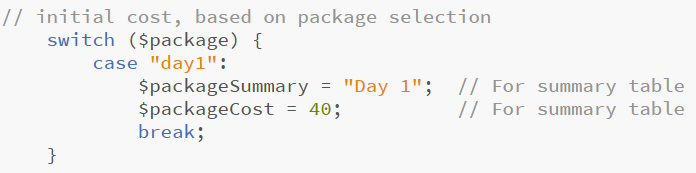
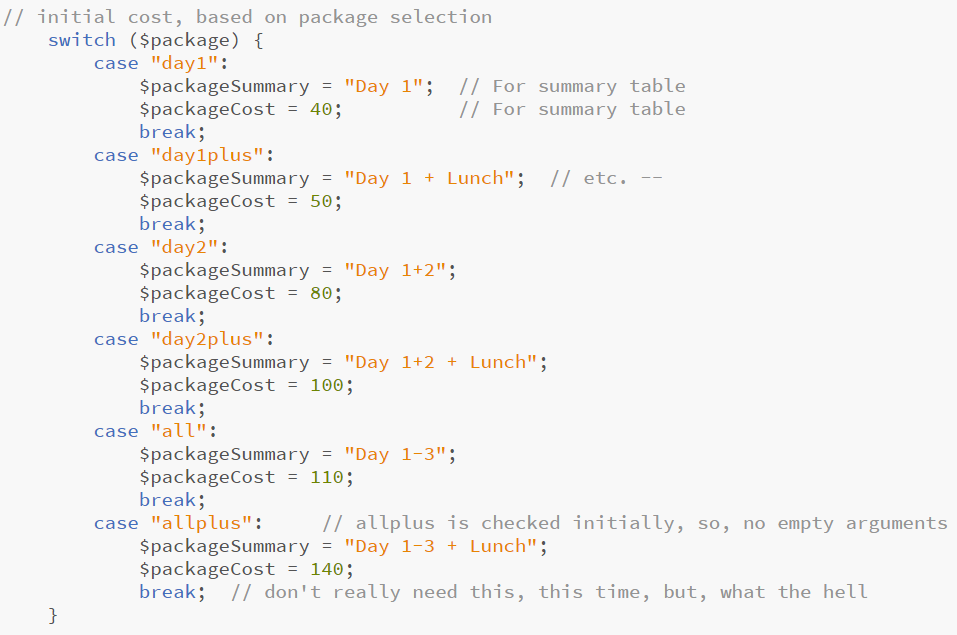
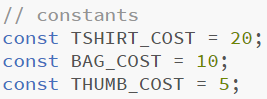
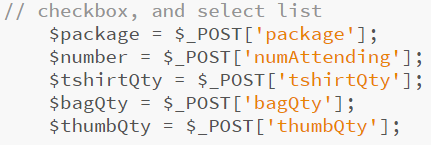
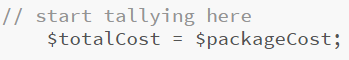
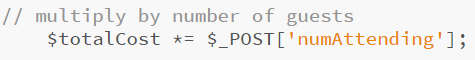
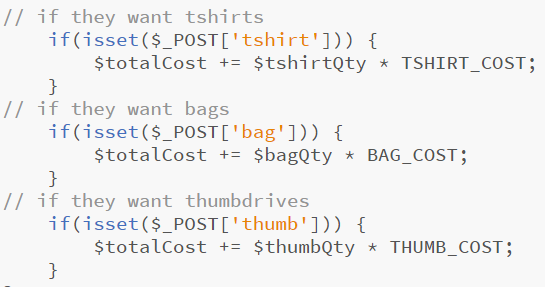
So now we have all of the input values. It's time to start tallying the cost
Notice here that I didn't store the $_POST value in a local variable. I could have, but it's the only place I need it and, since it's from a select list, it's safe to use without sanitizing
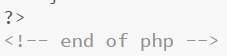
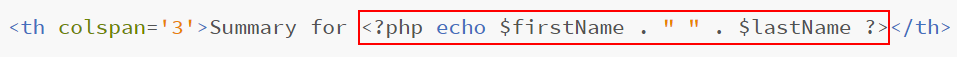
So this takes the $firstName and $lastName variables and injects their values into the output. You can see that the code in Line 152 creates the output table's header row
On further inspection, you can see that we use the <?php echo ?> instruction in Lines 155, 159, 164, 165, 170-176, 179-184, 191-196, 200-206, 212-218, 221-227, & 232 to construct the remainder of the table for the output page
Lines 170-176, 179-184, 191-196, 200-206, 212-218, 221-227 use embedded PHP to check whether the user chose to order optional items

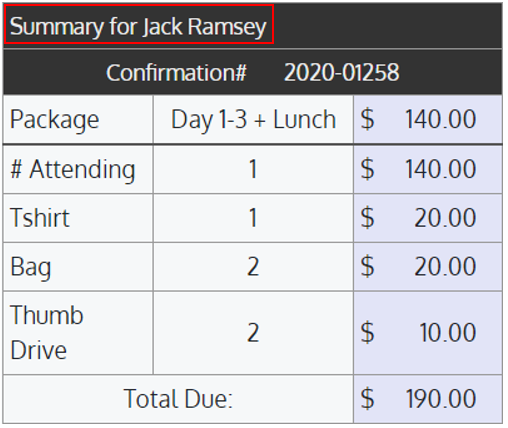
Troubleshooting with PHP can be a pain. Sometimes error messages don't display when it's run. But, remember our lecture on Developer Tools. Using the network tab will reveal error messages that don't make it to the display - From the DTs, when you run the erroring script, click on its filename to see what its output was
So this error message is telling you that firstName is undefined and it encountered the problem on Line 99 of confirm.php
If you run into errors, try to puzzle them out on your own. I'm happy to help, but you'll find that there's a pretty big sense of satisfaction in winnowing out your own bugs
Don't forget: When you make changes to your source files, you have to re-upload them to the server to test them
http://ramseyjw.csci1720.net/labs/lab10-php/registration.php) into a text file and upload it to the PHP folder on D2L
Have a nice day 😊